Secure Internet Architecture 6137029041 for Businesses presents a resilient, scalable framework that protects data, users, and applications across open and hybrid environments. It emphasizes zero-trust foundations, secure-by-default configurations, and continuous verification. Governance, risk, and performance are aligned with strategic tolerances to enable rapid innovation. Incident readiness and automated checks support measurable outcomes. The approach invites scrutiny of governance controls and enforcement mechanisms, leaving open questions about implementation breadth and operational impact.
What Secure Internet Architecture Means for Businesses
Secure Internet Architecture (SIA) provides a framework for designing and operating networks that inherently protect data, users, and applications across open and hybrid environments.
The approach clarifies governance, risk, and performance expectations, enabling scalable controls.
For businesses, this means codified data privacy practices and proactive threat modeling, aligning technology choices with strategic risk tolerances while preserving operational freedom and rapid innovation.
Practical Zero-Trust Foundations for Every Layer
Practical Zero-Trust Foundations for Every Layer establishes a layered security model that enforces continuous verification, least privilege, and dynamic access controls across networks, workloads, data, and interfaces.
The approach codifies zero trust fundamentals, enabling adaptive trust decisions, granular authorization, and ongoing risk assessment.
It emphasizes layered security design, policy-driven enforcement, and measurable security outcomes, aligning freedom with disciplined, verifiable protection.
Secure-by-Default Configurations and Verification
Aiming for a robust security baseline, secure-by-default configurations embed minimal-privilege, fail-safe defaults, and automated verification from deployment onward.
The approach enforces data integrity through strict access controls, consistent identity federation, and automated policy checks.
Encryption governance is baked into pipelines, while network segmentation isolates workloads, enabling rapid rollback, verifiable changes, and continuous compliance without impeding operational freedom.
Incident Readiness: Detection, Response, and Continuous Improvement
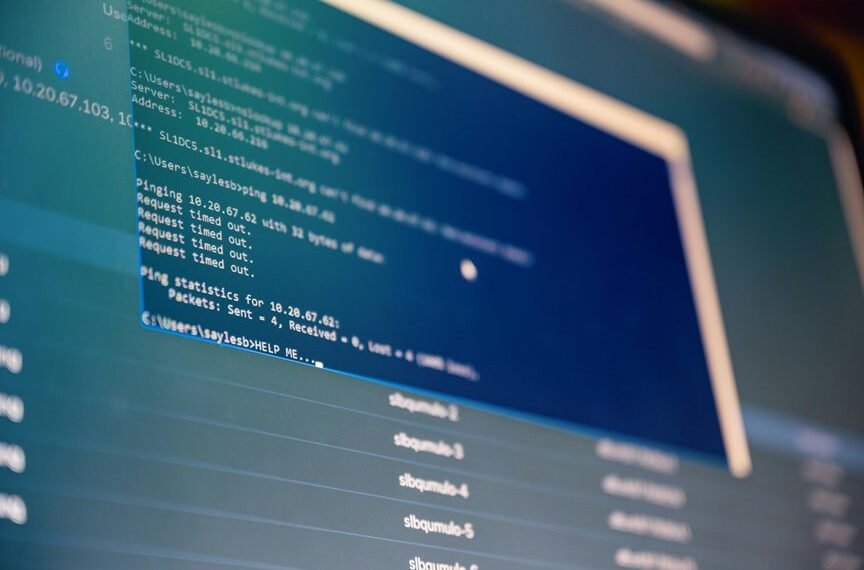
Incident readiness encompasses rapid detection, structured response, and intentional continuous improvement to minimize dwell time, containment risk, and business impact.
The approach uses security orchestration to coordinate tools, incident playbooks for repeatable actions, and response automation to accelerate containment.
Threat modeling informs detection strategies, while continuous improvement refines playbooks, reduces gaps, and sustains resilient, freedom-friendly operations.
Conclusion
In sum, Secure Internet Architecture 6137029041 equips businesses with a precise, scalable, zero-trust framework that harmonizes governance, risk, and performance. By embedding secure-by-default configurations, continuous verification, and automated policy enforcement, organizations can accelerate innovation without compromising security. Anticipated objection: “it’s too complex.” The approach reduces complexity through modular, policy-driven controls and automated checks, enabling measurable security outcomes with minimal operational burden and clear return on risk management.