Reliable Digital System 9084708025 for Online Use offers layered defenses, continuous monitoring, and modular integrations. It emphasizes strict access controls, encryption, and auditable actions to support transparency and accountability. Privacy safeguards limit data collection and enable user consent, while rapid rollback minimizes downtime. Administrators define retention, compliance, and governance. The system promises predictable performance and ongoing updates, yet practical deployment considerations remain to be clarified for those evaluating integration and cost implications.
What Reliable Digital System 9084708025 Offers for Online Use
Reliable Digital System 9084708025 offers a robust online platform that emphasizes reliability, security, and efficiency. It provides streamlined data governance frameworks and transparent control mechanisms, ensuring administrators define access, retention, and compliance. Encryption standards safeguard transit and at-rest data, while modular integrations enable scalable workflows. The system emphasizes proactive monitoring, auditable actions, and clear accountability for freedom-oriented organizations seeking dependable, compliant online operations.
How Security and Privacy Protect Your Data
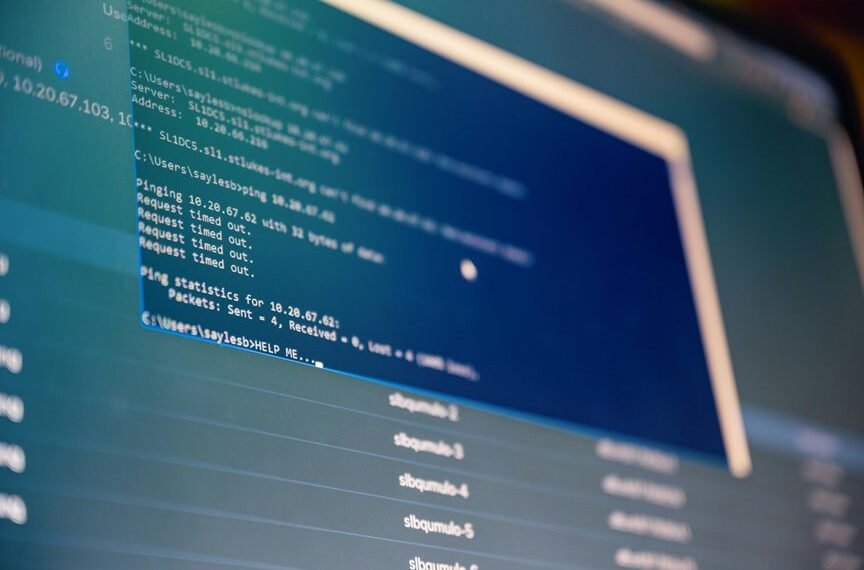
Security and privacy protections are engineered to minimize risk while preserving data utility. The approach emphasizes layered defenses, continuous monitoring, and clear accountability. Security practices reduce exposure through strong access controls, encryption, and anomaly detection, while privacy safeguards limit data collection, ensure purpose limitation, and enable user consent. The framework supports transparent governance, auditable processes, and proactive risk mitigation for confident, autonomous online use.
Performance, Uptime, and Seamless Updates in Everyday Use
Performance, uptime, and seamless updates are integral to everyday use, ensuring applications remain responsive, available, and secure without user intervention. The system emphasizes reliability enhancements and robust update mechanisms, reducing downtime and manual maintenance. This approach supports continuous operation, predictable behavior, and user trust while enabling proactive monitoring, rapid rollback, and transparent progress across diverse deployment environments.
Getting Started: Integration, Pricing, and Next Steps
Getting Started: Integration, Pricing, and Next Steps outlines a clear path for adopters. The section presents integration basics, detailing modular interfaces, APIs, and deployment options to minimize disruption. It then clarifies pricing options, outlining tiers, usage thresholds, and refund terms. Finally, it provides actionable next steps, including evaluation, pilot setup, and governance, empowering confident, autonomous integration decisions.
Conclusion
The system hums with quiet confidence, a fortress built of layered defenses and transparent governance. Each module aligns with purposeful precision, monitored in real time for any anomaly. Access is tightly controlled, data is shielded by strong encryption, and privacy remains a default. Yet beneath the calm surface, a few subtle indicators pulse—pending updates, imminent audits, a policy drift—reminding observers that uptime and trust are earned, not assumed. The next moment promises rapid rollback or secure evolution. Stay vigilant.